From Monolith to Microservices: A Step-by-Step Modernisation Guide
Modernising a monolithic application isn’t about chasing trends or rewriting everything from scratch. It’s about solving real problems - slow releases, risky deployments, poor scalability - without breaking systems that the business depends on every day.
Most organisations don’t have the luxury of stopping work to redesign their architecture. The monolith must keep running while changes are made around it. That’s why successful modernisation happens in steps, not in one big leap.
This guide walks through a step-by-step approach to moving from a monolith to microservices, using Azure as the foundation. The focus is on practical decisions, controlled risk, and incremental progress - starting small, learning quickly, and building confidence with each extracted service.
This isn’t a theory-heavy article or a “rewrite everything” story. It’s a realistic path for teams that need to modernise while staying live in production.
The Honest Truth About Monoliths
Before we talk about breaking things apart, let’s be clear: not every monolith needs to become microservices.
Some monoliths do their job well. An internal payroll system that’s stable and rarely changes? Modernising it may add more risk than value.
The real question isn’t “Should we migrate?”
It’s “What problem are we trying to solve?”
Modernisation starts to make sense when the monolith becomes a bottleneck - technically or organisationally. Common signals include:
Deployments turning into high-stress events involving multiple teams and late nights
Scaling one feature forcing you to scale the entire application (and pay for it)
New engineers taking months to become productive
Teams blocking each other because everything lives in the same codebase
Specific components needing stricter security, compliance, or isolation
If none of this applies, stop here. Microservices won’t help you.
But if several of these sound familiar, you don’t have a technology problem - you have an architectural constraint. And that’s exactly when a controlled move toward microservices starts to make sense.
Assessment: Know What You’re Really Dealing With
The most common failure in modernisation isn’t technology. It’s overconfidence.
Teams assume they understand the system because it’s familiar. But once you look closely, the “simple” application reveals hidden dependencies everywhere. The inventory module is tightly coupled to pricing. Pricing shares a schema with customer support. A background job updates all of it at 2 a.m. on Sundays. Pull one thread, and something unexpected breaks.
Before you change architecture, you need to understand reality - not diagrams, not assumptions.
Finding the Seams
Think of your monolith like a large piece of fabric. Cutting it randomly will ruin it. Cutting along the seams lets you separate it cleanly.
In architectural terms, those seams are bounded contexts - parts of the system that represent distinct business capabilities and can evolve independently.
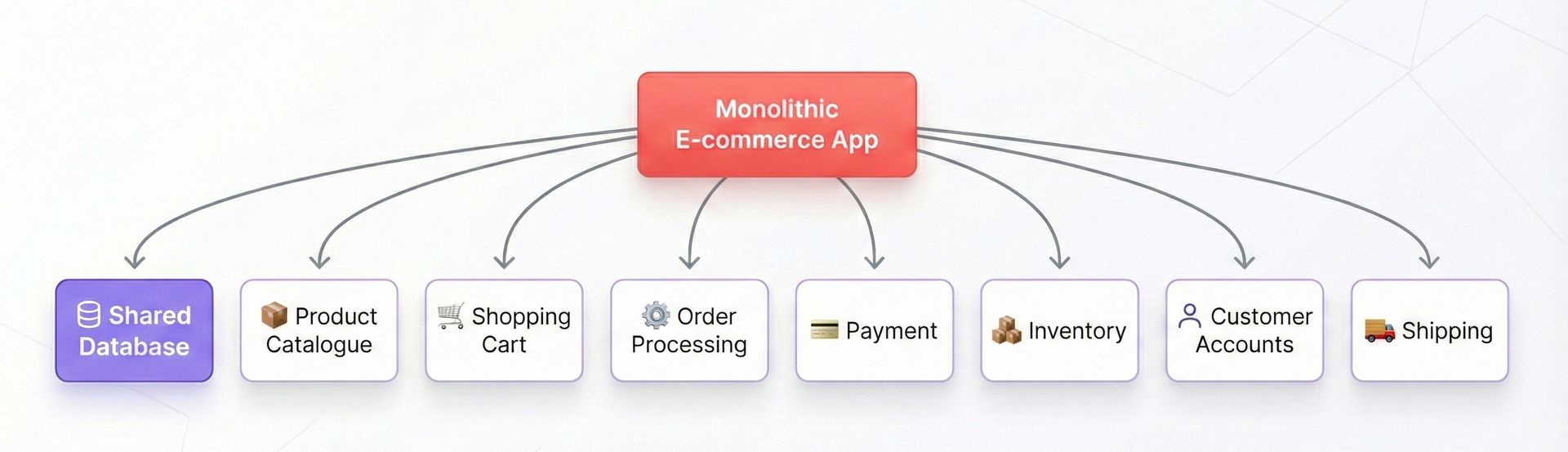
A typical e-commerce monolith often contains contexts such as:
Product catalogue
Shopping cart
Order processing
Payment handling
Inventory management
Customer accounts
Shipping and logistics
The hard part isn’t listing them. It’s proving they are truly independent.
Look for boundaries where:
Different teams naturally own the functionality
Changes in one area rarely require changes in another
The business already talks about them as separate concerns
If you can’t clearly identify these seams, you’re not ready to extract microservices yet. Assessment isn’t a formality - it’s the foundation the entire migration stands on.
The Dependency Map
Once you’ve identified candidate services, the next step is unglamorous - but non-negotiable: map the dependencies.
Create a simple dependency map - nothing fancy. A spreadsheet is enough. For each potential service, document:
The data it owns and the data it reads from elsewhere
The internal services it calls
The services that call into it
The database tables or schemas it touches
The external systems it integrates with
This exercise will surface uncomfortable truths: hidden coupling, shared data models, and “temporary” integrations that became permanent years ago.
That’s a good thing.
A clear dependency map turns guesswork into a plan. It tells you which services can be extracted safely, which ones need refactoring first, and which dependencies must be broken before you move anything to Azure.
This isn’t documentation for documentation’s sake.
It’s your migration roadmap.
Azure’s Microservices Toolkit: Choosing Your Foundation
Azure gives you multiple ways to run microservices - and this choice has long-term consequences. It affects how fast teams deliver, how much operational effort you carry, and how easily the platform scales as the architecture evolves.
Let’s focus on the options that matter in real modernisation projects.
Container Apps vs AKS vs App Service vs Functions
Azure Container Apps is the most balanced option for most teams modernising a monolith. It’s built on Kubernetes but removes the operational burden. You get containers, autoscaling, event-driven execution, and native Azure integrations - without managing clusters or nodes.
The trade-off is intentional: no direct access to Kubernetes APIs. For most migrations, that’s a feature, not a limitation. This is often the sweet spot.
Azure Kubernetes Service (AKS) gives you full Kubernetes control and direct API access. Choose AKS when you genuinely need Kubernetes-specific capabilities - custom operators, advanced networking, service meshes, or when you already run Kubernetes at scale. If the primary reason is familiarity or future-proofing, pause. AKS adds power, but it also adds overhead.
Azure Functions fits naturally into microservices architectures where services react to events rather than serve constant traffic. Processing queue messages, handling webhooks, responding to file uploads - Functions can be simpler and more cost-effective than running always-on containers. A mature architecture often mixes containers and functions, rather than forcing everything into one model.
App Service remains a valid choice, especially for .NET or Node.js services that don’t need containerisation. One service per App Service, minimal operational effort, predictable behaviour. You trade off container portability, but for many teams, that’s an acceptable compromise.
The Kubernetes API Question
This is the real decision point.
If your architecture directly depends on Kubernetes APIs - custom controllers, CRDs, or Kubernetes-native tooling - AKS is the right choice.
If your goal is simply to deploy containers, scale them, and integrate with Azure services, Container Apps removes unnecessary complexity while still giving you Kubernetes benefits under the hood.
Start simple. Choose the least complex platform that supports your needs today. You can always move to AKS later. Starting with AKS when you don’t need it is much harder to unwind.

Communication: How Services Talk
In a monolith, components communicate by calling methods in the same process. It’s fast, reliable, and invisible.
Microservices don’t have that luxury. Once services are split, every interaction becomes a network call - and how you design those calls determines whether your architecture is resilient or fragile.
On Azure, service communication usually falls into two patterns.
Synchronous Communication
Synchronous communication uses REST APIs or gRPC. Service A calls Service B and waits for a response. This is simple to reason about and easy to debug.
In Azure, Azure API Management typically sits in front, handling routing, authentication, rate limiting, and versioning.
The downside is coupling. If Service B is slow or unavailable, Service A feels it immediately. Used excessively, synchronous calls recreate monolith-style dependencies - just over HTTP.
Asynchronous Communication
Asynchronous communication relies on messages and events. Service A publishes an event to Azure Service Bus or Azure Event Grid, and Service B processes it when ready.
This decouples services and improves resilience. Systems scale better, failures are isolated, and services can evolve independently. The trade-off is complexity: eventual consistency, retry handling, and harder end-to-end tracing.
The Right Mental Model
Synchronous communication is a phone call - you need an answer now, and both parties must be available.
Asynchronous communication is email - you send the message, carry on with your work, and trust the system to deliver it.
Practical Guidance
Use synchronous calls only when you truly need an immediate response. Prefer asynchronous messaging for workflows, state changes, and integration between domains.
If everything is synchronous, you haven’t really escaped the monolith - you’ve just distributed it.
The Strangler Fig Pattern: Your Best Friend
This is where architecture theory meets delivery reality.
You don’t switch off a monolith on Friday and go live with microservices on Monday. Anyone who suggests that hasn’t run a production system. The Strangler Fig pattern exists precisely because real systems can’t afford big-bang rewrites.
The idea is straightforward: you gradually replace parts of the monolith with new services while the original system continues to run. Traffic is incrementally redirected to the new components. Over time, the monolith shrinks until it can be safely retired.
No downtime. No heroics. No rewrites driven by optimism instead of evidence.
Setting Up the Foundation
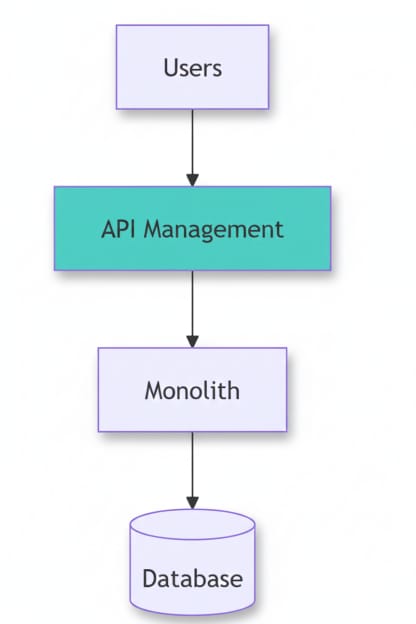
The first step is control of traffic.
Place Azure API Management in front of the monolith. From this point on, every external request flows through the gateway.
Initially, the gateway does nothing clever. It simply forwards all requests to the existing application. Users see no change. The system behaves exactly as it did before.
This is critical.
By introducing the gateway first, you decouple routing from implementation. Once that control plane is in place, you can start redirecting specific endpoints or operations to new microservices - one capability at a time - without touching clients or breaking contracts.
At this stage, you’re not modernising functionality.
You’re creating options.
And that’s what makes the Strangler Fig pattern so effective: it lets you modernise safely, incrementally, and on your own terms.
Extracting Your First Service
Your first microservice should be boring. That’s not a criticism - it’s a survival strategy.
Pick something simple, stable, and low-risk. The product catalogue is often a strong candidate: it’s read-heavy, changes infrequently, and is consumed by many parts of the system. That combination makes it valuable to extract, yet forgiving if something goes wrong.
Avoid anything transactional or state-heavy for your first move. You’re proving the migration approach, not testing your tolerance for outages.
The First Extraction (Done Properly)
Build the new service around a clearly defined API and deploy it to a managed platform such as Azure Container Apps or Azure App Service, depending on your stack and maturity.
For the first iteration, it’s acceptable to point the service at the same database as the monolith. This is a conscious compromise - not the end state. The goal here is to validate routing, deployment, monitoring, and rollback, not to solve data ownership on day one.
Test it thoroughly. Treat it as production from the start.
Once you’re confident, update Azure API Management to route product catalogue requests to the new service instead of the monolith. Clients remain unchanged. If something goes wrong, routing can be reverted in minutes.
That’s the key win.
At this point, you haven’t “modernised everything” - but you’ve proven that:
Traffic can be redirected safely
Services can be deployed independently
The monolith can be reduced without breaking consumers
From here, momentum builds. Each successful extraction lowers risk for the next one.

If something goes wrong, you flip the routing back. From the user’s point of view, nothing ever happened.
Dealing with Data
This is the hardest part of the journey - and the part most teams underestimate.
In the end, every microservice should own its data. But trying to migrate application logic and databases at the same time is how outages happen. You separate behaviour first, then data - never both together.
The pattern is deliberate and slow by design.
The Data Decoupling Pattern
For each extracted service, the transition typically looks like this:
Read from the shared database
The new service initially reads from the existing schema. In some cases, dual reads are used to compare behaviour.Write to both databases
The service writes to the shared database and its own dedicated store. This keeps the system consistent while ownership shifts.Validate consistency over time
Data is compared, reconciled, and monitored. This is where most issues surface - and why patience matters.Switch reads to the service-owned database
Once confidence is high, the service stops reading from the shared schema.Stop shared writes
Writes to the monolith’s database are removed for that domain.Retire shared tables
Only after everything is stable are the old tables removed.
There are no shortcuts here.
This process takes weeks - or months - per service. That’s normal. Anyone promising a faster path is either skipping validation or ignoring failure modes.
Data separation isn’t glamorous, but it’s what turns a distributed monolith into an actual microservices architecture.
Get this wrong, and everything else eventually collapses.
The Reality Check No One Talks About: Cost
Let’s be direct: this will cost more at first.
Running many small services is more expensive than running one large application. Each service needs compute, storage, networking, and monitoring. Your Azure bill will go up.
That’s the price of flexibility.
What you gain is control. Services scale independently. A product catalogue can scale for a sale without scaling the entire platform. Over time, that control can reduce waste - but you’ll need to justify the initial increase to finance.
Keeping Costs Under Control
Use Azure Container Apps autoscaling, including scale-to-zero
Share infrastructure where it makes sense (for example, multiple services on one AKS cluster)
Use Azure reservations for steady workloads
Monitor aggressively and delete unused resources
Microservices don’t save money by default. They buy you speed, resilience, and flexibility. Cost optimisation comes later.
Security in a Distributed World
The security model changes completely.
In a monolith, once a request gets past the front door, it’s effectively trusted. In a microservices architecture, every service-to-service call crosses a security boundary - and must be treated as untrusted by default.
Azure simplifies this with Azure Managed Identities. Each service gets its own identity, and Azure issues and manages access tokens automatically.
No secrets in configuration files.
No credentials to rotate.
No shared identities across services.
Each service authenticates to exactly what it needs - and nothing more.
In a distributed system, security isn’t a perimeter.
It’s enforced at every hop.

Network Security Groups, private endpoints, and Azure API Management policies add multiple layers of defence.
Yes, this is more complex than a monolith - but it’s also far more secure when done properly.
Final Thoughts
The move from monolith to microservices isn’t a sprint - or even a marathon. It’s more like renovating a house while you’re still living in it.
Start with one service. Learn from it. What worked? What didn’t? Then do the next one. Some organisations take years to complete the journey, and that’s perfectly fine. In many cases, the monolith never fully disappears - it simply becomes another service in the architecture.
What matters is having a clear direction, taking deliberate steps, and being honest about the trade-offs. Microservices aren’t magic, and they’re not always the right answer. But when they are, Azure gives you a strong foundation to build on.
The real question isn’t whether to migrate - it’s whether you’re ready for the journey.
If you are, take the first step. Extract one service. Learn from it. Then choose the next.
That’s how modernisation actually succeeds - one careful step at a time.
If you found this useful, tap Subscribe at the bottom of the page to get future updates straight to your inbox.